Web & Mobile Apps Tested
800+
Networks & Servers Tested
6,000+
Vulnerabilities Eliminated
15,000+
Yes, we are CREST accredited
Our core team is based in Singapore and consists of CREST certified penetration testers who are also Offensive Security Certified Professional (OSCP) certified. The team has delivered numerous penetration testing projects for customers in Singapore and other locations, from large multinational enterprises to small and medium business, and across various industries.
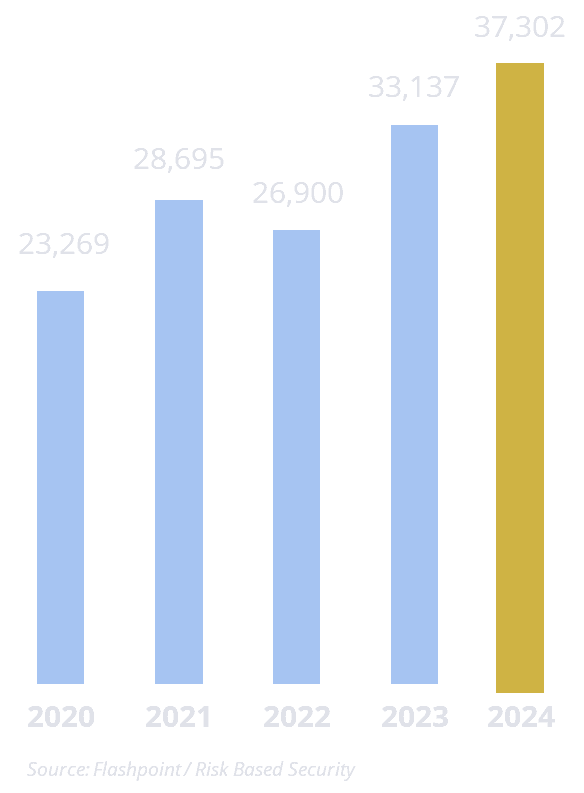
Almost 150K reported vulnerabilities in last 5 years
Almost 150,000 vulnerabilities were reported for commonly used software over the last five years. This is an average of 3.4 vulnerabilities published every hour. In 2023 alone, half of all vulnerabilities were given a High or Critical severity rating, of which, 55% can be remotely exploited and 28% have known public exploits.
In a 2020 study, 14% of vulnerability exploits were publicly available before the vendor released security patches, and another 23% were available within the first week.

Vulnerability Assessment
Expose hidden risks before attackers do

Use a vulnerability scanner to analyze your environment for vulnerabilities. The scan should include all your servers, network devices whether they are located within your premises or hosted in the cloud.
Best practices suggest running vulnerability scans at least on a quarterly basis.

Penetration Test
Turning vulnerabilities into actionable insight

A penetration test simulates the tools and techniques of an attacker to detect and exploit vulnerabilities. This approach conducted by a skilled professional helps you identify possible attack routes and securities vulnerabilities that may not be found from vulnerability assessments.
Most industry standards recommend a penetration test on your network, web and mobile applications at least once a year and after major changes.
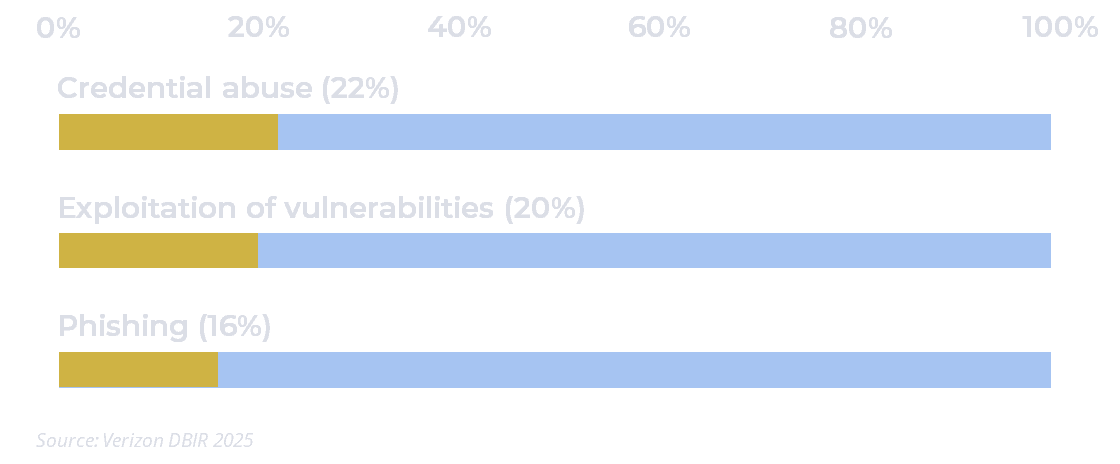
42% of data breaches involved hacking
According to Verizon’s 2025 Data Breach Investigations Report, 42% of the more than 12,000 data breaches analyzed in 2024 involved hacking. The malicious activities include exploiting vulnerabilities and using stolen credentials.

Configuration Review
Harden from the inside before attackers get in

Configuration reviews can help ensure that servers and network devices are securely configured, and alert you to any errors and misconfigurations.
While vulnerability assessments and penetration testing provides an analysis from an external point of view, configuration reviews provide an in-depth view from within your servers and network devices.

Code Analysis
Secure code. Secure applications. Secure business.

Security weaknesses introduced by software developers may not be easily detected by vulnerability assessments and penetration testing.
Reviewing the source code of your custom-built applications for vulnerabilities or malicious code helps prevent security issues from going into production and is an important part of a secure development lifecycle.

Adversarial Emulation
Experience the attack before it happens for real

Simulate real-world attack chains—phishing to gain a foothold, red-team tactics to exploit it, and purple-team collaboration to validate detection and response—so you can test the whole kill chain under controlled conditions.
Running these simulations reveals gaps people and technology alone miss, sharpens detection playbooks, and converts failures into measurable improvements in training, tooling and incident response.





